Many clients have recently asked us for our top recommendations for project management software and tools. Our experience with these tools is mostly derived from helping our clients incorporate them into their processes while we add the accountability layer that is often missing in these tools to make sure things get done.
Insights
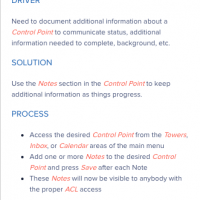
Software companies are trying to figure out how to empower their users so they can figure things out on their own. Intuitive graphical user interfaces, embedded help, FAQs and user forums are some of the concepts that have developed recently to help software companies scale more efficiently.
Executives, decision makers, and management in general have a finite amount of “Management Attention Units” (MAUs). So, what are MAUs anyway? We use this general term to refer to time used by management to carry out core supervisory duties. Management’s time – a very valuable and finite commodity.
Why do some employees seem always to get things done on time and as expected, while others struggle? Is it in their DNA? Is it an organizational culture that condones missed deadlines so that some people do not feel the pressure to perform as well? Are incentives, like bonuses, or penalties, like losing a job, accomplishing their objectives?
When a company is charged with financial statement fraud, the first question asked is “Where were the auditors?”
But auditors can only insure accurate financial reports in a robust business environment where every stakeholder has bought into the importance of internal control procedures and their documentation.
Creating an internal control integrated framework over subjective and complex accounting areas such as revenue recognition, loan impairment and valuation is especially challenging, and insufficient internal control procedures can leave an organization dangerously open to fraudulent financial reporting.
Have you come to terms with the fact that accountability is the missing element to drive your team to excellence?
Law firms continue to base their entire business model on tracking billable hours. More often than not, clients feel they have little control of what a specific legal proceeding will cost. Why is it so hard for law firms to offer fixed deliverable-based pricing?
Ask anyone in your office how they feel about meetings, and you are likely to get passionate responses on both sides of the aisle.
In the wake of the UK Parliament’s recent network security attack, it’s clear that no matter how well-designed our IT security systems and internal controls are, there’s always a risk of your organization falling victim to a cyber threat.
Making the transition from being an entrepreneur-led business to one that operates as an “institution” is not easy. A business that deals with everything that comes their way in a reactive, ad-hoc, team-based manner is not scalable. So, start with clearly defining and communicating a function-based org chart that nicely follows your value-chain.