The Employee Offboarding Process and IT Security
The worldwide cyberattacks in the news lately have worried businesses and individuals alike.
The ransomware attacks Petya and WannaCry have affected commercial businesses, governmental entities, and individuals by the thousands. But while the media focuses on these external attacks, internal network security threats remain one of the most common problems in security management.

The Threat
The Dell End-User Security Survey 2017 found that “72 percent of employees are willing to share sensitive, confidential, or regulated company information,” and that “more than one in three employees (35 percent) is willing to take corporate information with them when leaving a company.”
Uber was recently sued for the alleged theft, by an executive at a subsidiary company, of trade secrets when he left that company. And in June Verelox, a Netherlands based web host, had to temporarily shut down all services after a former administrator deleted all customer data and wiped most of the servers.
A Key Weakness
How can a business prevent a former employee from using their access to delete data or to steal software, data, customers or intellectual property?
A critical, and often overlooked, area where a business needs to develop strong policies and procedures is employee offboarding.
What Are Some of These Employee Offboarding Policies?
Teams across the organization should collaborate to identify threat areas when employees leave the company and should develop the necessary policies to mitigate network security threats.
Get everyone’s feedback on who has access to internal information and how they access that data – office computers, personal laptops, phones, etc.
What is your company’s BYOD policy? Keep track of licenses and system access information for each employee. Create a list that can be activated to immediately stop access to company data once an employee termination happens.
Hold employees accountable for the consistent execution of these off-boarding policies and procedures.
Who Needs to Know About an Employee Termination?
HR is no longer the only department that should be involved in an employee’s termination. It is essential that all departments coordinate and work together before, during and after the offboarding process.
The IT department should be notified even before the termination meeting with the employee so that they can initiate the process of terminating access on a timely basis.
How Do We Make Sure Nothing Falls Through the Cracks?
Never underestimate the power of a good checklist. Today more than ever, it is essential that every step of the offboarding process is carried out and documented, and that every player relevant to the process is held accountable for the timely execution of each step.
An accountability tool like CommandHound can be used to tightly monitor the on time execution of the off-boarding process.
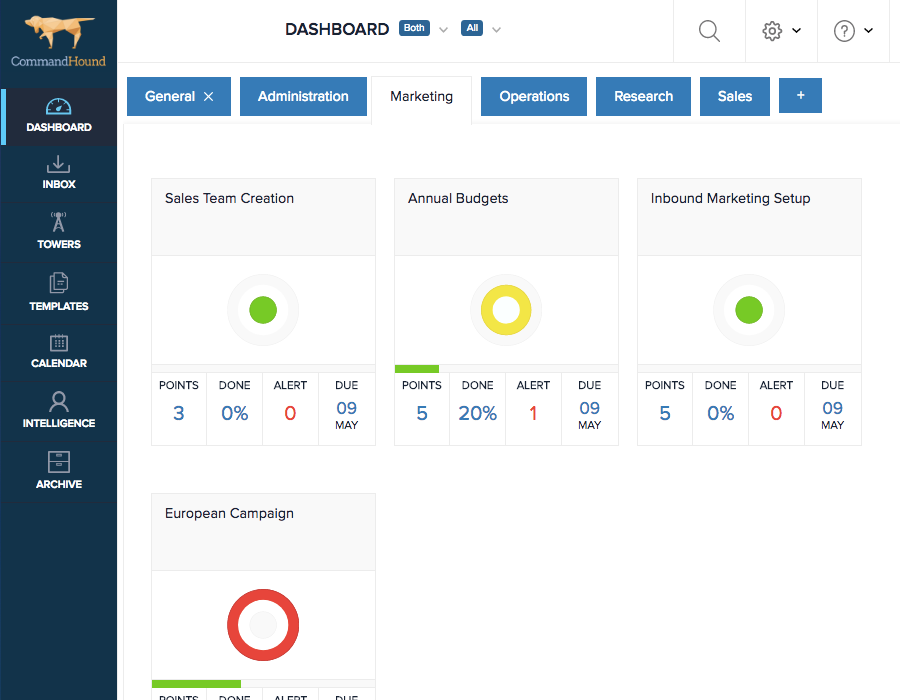
An employee accountability tool like CommandHound will help your HR team enforce important company policies.
CommandHound not only allows you to define an employee offboarding process to make sure all steps are consistently carried out, but it also sends reminders, escalates things, and monitors things to make sure things get done as expected.
Would you like to learn more?
